 I’ve been selected as a breakout speaker for the 2011 ASUG SAP BusinessObjects User Conference, October 9-12, 2011 at the Swan and Dolphin Resort at Walt Disney World in sunny Orlando, Florida. This year I’ll be speaking about securing the new UNX universes created by the SAP BI 4.0 Information Design Tool. Here is the abstract for my session.
I’ve been selected as a breakout speaker for the 2011 ASUG SAP BusinessObjects User Conference, October 9-12, 2011 at the Swan and Dolphin Resort at Walt Disney World in sunny Orlando, Florida. This year I’ll be speaking about securing the new UNX universes created by the SAP BI 4.0 Information Design Tool. Here is the abstract for my session.
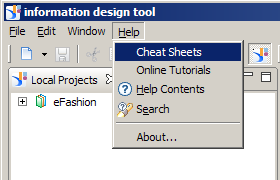
Do you need to tailor semantic layer security to specific users or groups within your organization? Attend this session to learn about security profiles in the new Information Design Tool in SAP BusinessObjects Business Intelligence 4.0. Understand how applied restrictions can control objects, rows, query types, and connections. See live demonstrations on how to use each type of restriction and the effect it has on end users’ interactive experience.
Key Learning Points:
- Find out how to secure and personalize your users’ ad-hoc query experience.
- Learn how to secure semantic layer in the information design tool.
- Gain confidence in the security model using built-in testing tools.
My session occurs on Tuesday, October 11, 2011 from 4:00 PM – 5:00 PM. I hope to see you there!
UPDATE: The slide deck is available on my presentations page.
Learn more about the 2011 ASUG SAP BusinessObjects User Conference
Learn more about the Walt Disney World Swan and Dolphin Resort
Learn more about Walt Disney World


Hi Dallas,
Congrats on your selection! I look forward to seeing the slidedeck 🙂
– Josh
Dalla
Have you encountered/implemented a way of using the @variable(BOUSER) for row level security which cannot be worked around if the user has Edit SQL allowed. My concern is that anything we do in the universe can be circumvented by Power users who have Edit SQL, and so we would need to put such row level security down in the DB i.e. after the SQL gets submitted. But then one doesn’t have access to the BOUSER variable. Seems like a rock or a hard place!
Thanks
It is a rock and a hard place, unfortunately. You must choose.